- IP...
- ISP...
- Location...
- Status...
01
Traditional Viruses
Traditional viruses are malicious programs that replicate themselves by modifying other computer programs and inserting their own code. They can cause a wide range of issues, from minor annoyances to total system failure.
02
Spyware
Spyware is a type of malware that is installed on a computer without the user's knowledge. It secretly monitors the user's activities, such as browsing history, keystrokes, and login credentials, and sends this information to a third party.
03
Adware
Adware is software that automatically displays or downloads advertising material, such as banners or pop-ups, when a user is online. While often just annoying, some adware can also track your data and slow down your system.
04
Ransomware
Ransomware is a type of malware that encrypts a victim's files. The attacker then demands a ransom from the victim to restore access to the data upon payment. We prevent these attacks before they can start.
05
Trojans
Trojans, or Trojan Horses, are malicious programs that disguise themselves as legitimate software. Once installed, they can give hackers unauthorized access to your system, allowing them to steal data or install other malware.
06
Keyloggers
Keyloggers are a type of surveillance software that has the capability to record every keystroke you make to a log file. This can include sensitive information like credit card numbers and passwords.
07
Rogues
Rogue security software is a form of malicious software and internet fraud that misleads users into believing there is a virus on their computer and manipulates them into paying for a fake removal tool.
08
Rootkits
Rootkits are a collection of computer software, typically malicious, designed to enable access to a computer or an area of its software that is not otherwise allowed and often masks its existence.
09
Worms
Worms are a type of malware that can self-replicate and spread independently across a network. Unlike viruses, they don't need to attach themselves to a host program or file, making them particularly dangerous for network stability.
10
Botnets
A botnet is a network of private computers infected with malicious software and controlled as a group without the owners' knowledge, e.g., to send spam or launch cyberattacks.
11
Pharming Attacks
Pharming is a cyberattack intended to redirect a website's traffic to another, fake site. It can be conducted either by changing the hosts file on a victim's computer or by exploitation of a vulnerability in DNS server software.
12
Phishing Attempts
Phishing is a method where cybercriminals impersonate legitimate institutions via email or text to steal sensitive information such as login credentials and financial details.
13
XSS Attacks
Cross-Site Scripting (XSS) is a vulnerability where malicious scripts are injected into trusted websites. We monitor and block these scripts to prevent attackers from stealing your session cookies or other private data.
Why do I need it?
There are over 350,000 pieces of malware are detected every day and a record-breaking 10.52 billion malware attacks in 2018. These numbers are growing and growing year over year. In fact, the estimated cost of ransomware attacks is $20 billion in 2020.
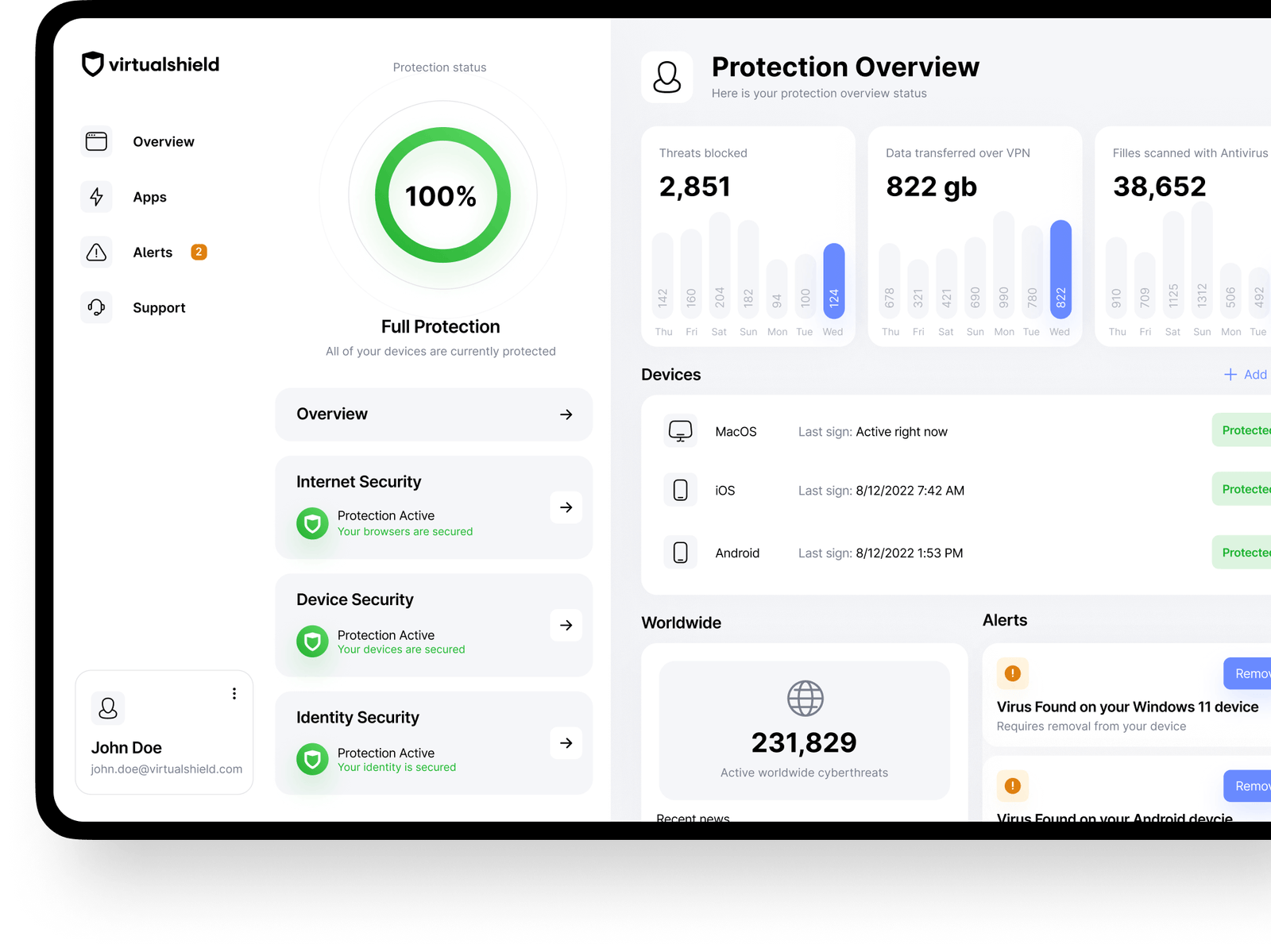
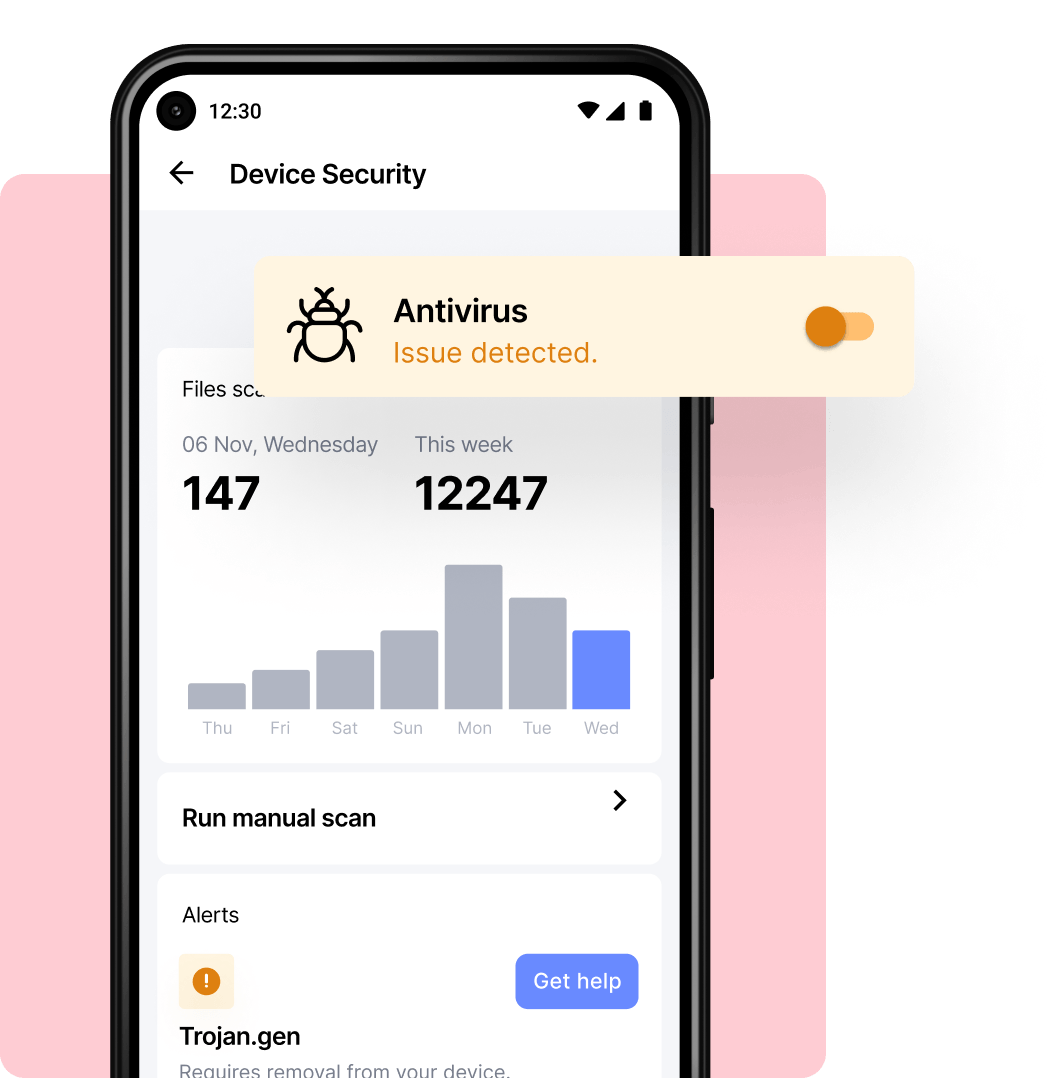
How does it work?
Antivirus software works in real-time to block viruses and malware and prevent hackers from taking over your computer remotely. All you have to do to get protected is download the respective PremiumLiveVPN application for your platform, install it, and log in. PremiumLiveVPN will work in the background to ensure that you are protected.
Who can use it?
Antivirus is important for all computer and mobile users. If you have a PC or Android device, you are more at risk than Mac and iOS users. If you use a computer, browse the internet and download files, then you need antivirus software to ensure your protection.

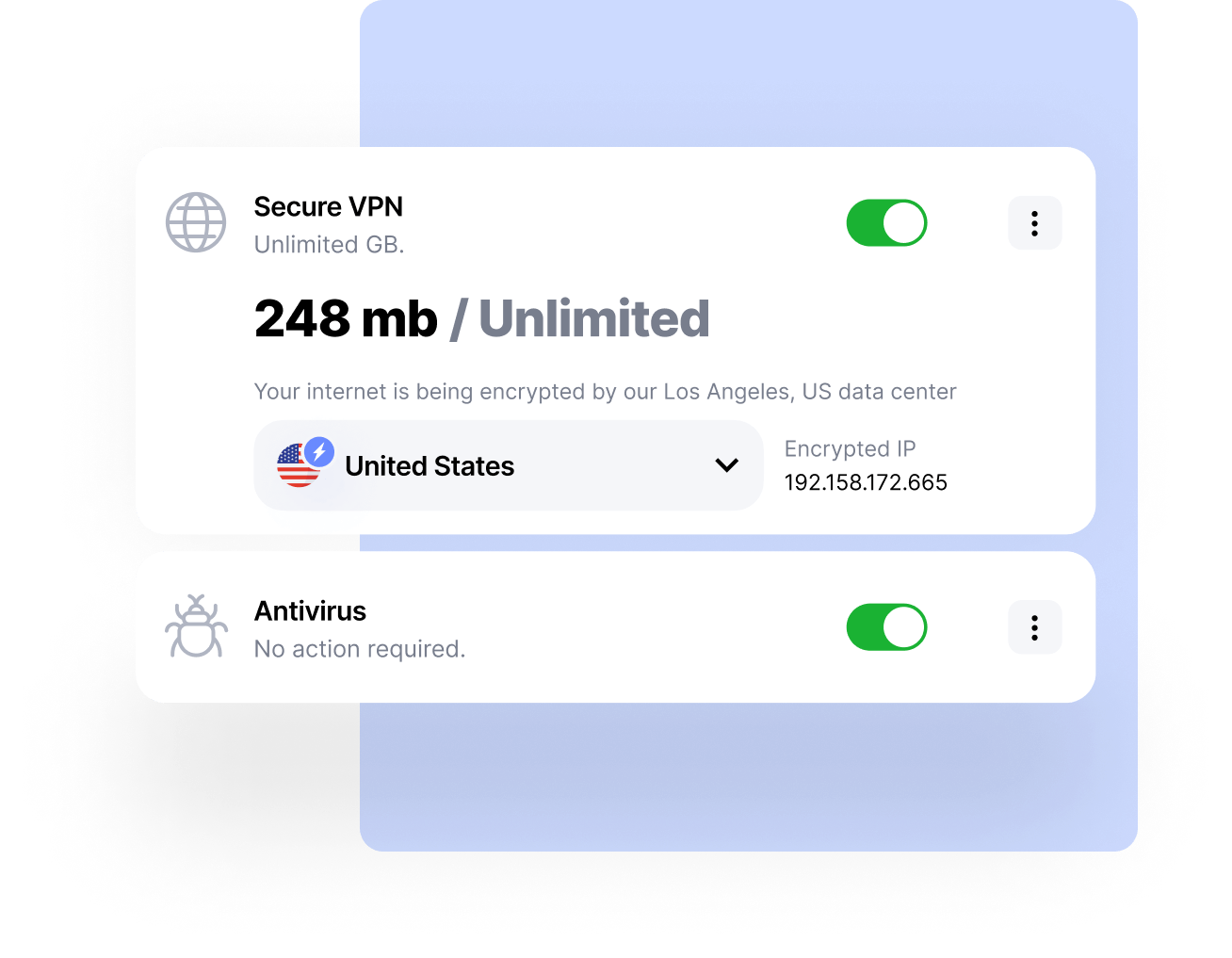
60 Days Risk Free!
- 7 Days Free Trial
- 60 Days Money-Back Guarantee
Get complete protection with PremiumLiveVPN.
- Unlimited devices
- Easy to use
- Cross platform support
- Next-gen technology
- 256-bit encryption